WhiteOwl Enterprise Network Observability Use Cases
WhiteOwl enables enterprises to gain deep visibility, accelerate troubleshooting, and proactively manage risk across complex, hybrid environments by unifying flow, metrics, logs, synthetic testing, and device configuration intelligence.
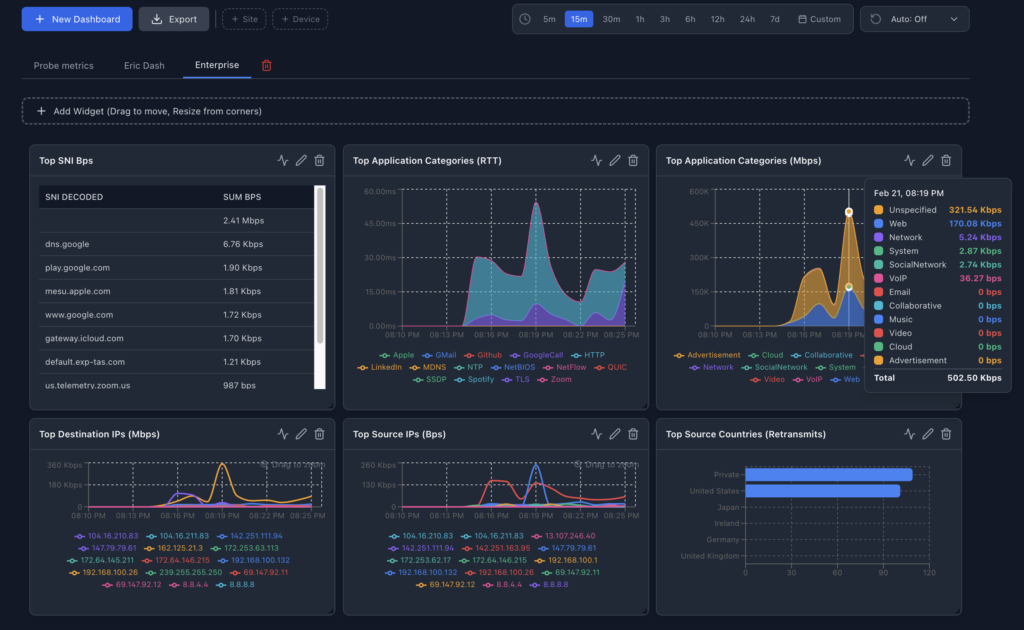
Best Flow (Traffic & Application Visibility)
Primary Value: Understand who is talking to whom, how much, and why it matters—across data centers, campuses, and cloud edges.
Enterprise Use Cases
- Application Performance Analysis
- Identify top talkers, bandwidth hogs, and unexpected traffic patterns
- Correlate application slowdowns to specific flows or network segments
- East–West Traffic Visibility
- Detect lateral movement and abnormal service-to-service communication
- Support Zero Trust and micro-segmentation initiatives
- Capacity Planning & Cost Optimization
- Track long-term traffic growth trends
- Validate WAN, SD-WAN, and cloud egress spend
- Security & Threat Investigation
- Identify suspicious traffic patterns without packet capture
- Support SOC investigations with historical flow evidence
- TCP/IP Performance, SNI decoded and microburst detection using the WhiteOwl
Who Cares
Network Engineering, Security Operations, Cloud & Platform Teams
SNMP (Device Health & Performance Monitoring)
Primary Value: Real-time and historical insight into the health of network and infrastructure devices.
Enterprise Use Cases
- Proactive Fault Detection
- Monitor interface errors, drops, CPU, memory, and power health
- Detect degradation before users notice
- SLA & Availability Monitoring
- Validate uptime and performance commitments
- Provide hard data for vendor accountability
- Root Cause Analysis
- Correlate device resource spikes with traffic, logs, or config changes
- Hardware Lifecycle Management
- Identify aging or underperforming devices
- Support refresh and consolidation planning
- Topology visualization and drill-down.
- View who is connected to who.
- Color coded devices to see whats up, down or having problems.
Who Cares
Network Operations (NOC), Infrastructure Teams, IT Leadership
Synthetic Monitoring (User Experience Validation)
Primary Value: Measure what users should experience—even before they complain.
Enterprise Use Cases
- Business-Critical Application Monitoring
- Continuously test login, API, and transaction workflows
- Detect outages or slowdowns in SaaS, internal apps, and hybrid services
- Change Validation
- Confirm performance before and after network, firewall, or app changes
- Geographic & Remote User Experience
- Monitor application reachability from branch offices and remote locations
- Vendor & Cloud Dependency Monitoring
- Track third-party service availability and latency over time
Who Cares
Application Owners, Digital Experience Teams, IT Operations
Logs (Event, Security & Operational Intelligence)
Primary Value: Turn noisy logs into actionable operational and security insights.
Enterprise Use Cases
- Faster Incident Investigation
- Correlate logs with flows, SNMP metrics, and synthetic failures
- Reduce MTTR by seeing the full story in one place
- Security Event Analysis
- Detect authentication failures, policy violations, and abnormal behavior
- Support threat hunting and forensic investigations
- Compliance & Audit Support
- Centralized log retention and searchable history
- Evidence for audits and incident reviews
- Change & Configuration Visibility
- Track who changed what, when, and what broke afterward
Who Cares
Security Teams, IT Operations, Compliance & Risk
Device Configurations (Governance & Change Control)
Primary Value: Reduce outages and security risk caused by misconfigurations and drift.
Enterprise Use Cases
- Configuration Drift Detection
- Identify deviations from approved baselines
- Enforce standardization across environments
- Change Impact Analysis
- Correlate config changes with performance degradation or outages
- Backup & Recovery
- Maintain versioned config backups for rapid rollback
- Security Posture Management
- Detect weak settings, deprecated protocols, and policy violations
- Support internal security standards and regulatory requirements
Who Cares
Network Engineering, Security Architecture, Compliance
Why This Matters for Enterprises
- Unified visibility across network, infrastructure, and application layers
- Reduced mean time to resolution (MTTR) through correlation, not silos
- Lower operational risk from blind spots and unmanaged change
- Data-driven decisions for capacity, security, and modernization
